How does PTAS actually work?
As more of our clients move to adopting PTAS for their infrastructure testing due to its cost effective commercials, fast-paced delivery and ability to conduct more regular assessments, we deep dive into how the service works, and the value it is showcasing.
Today, organisations face various challenges when approaching penetration testing.
- Seeking an available provider in relevant timelines;
- Verifying the experience of the consultant delivering the test;
- Ensuring consistent, critical communication between the consultant and client point of contact;
- Having complete assurance that a penetration test, rather than a vulnerability scan, is what is being delivered; and
- Certainty that the output of the test and quality of reporting will be at the correct standard and will provide meaningful, actionable intelligence which the operational and business leadership can consider and action to enable the growth and future success of the organisation.
We have already outlined the cost (70%+) and time (hours Vs weeks) savings achieved through PTAS compared to traditional manual approaches. What are clients receiving through this service though? Some examples are listed below:
Continuous security assessments to understand your risks to cyber attacks in near real-time.
Traditional assessments only allow organisations to demonstrate a point-in-time snapshot of the environment. Amicis enable continuous risk management by allowing you to perform full-scale network penetration tests and vulnerability assessments with a few clicks.
Meet compliance requirements with more scheduling flexibility and real-time alerts.
Businesses can satisfy compliance requirements with more scheduling flexibility and real-time alerts. Amicis provide complete flexibility in schedule, alerting, real-time activity tracking, as well as segmentation testing to confirm isolation of sensitive networks. In addition to ensuring compliance readiness, Amicis also tests for security deficiencies that deviate from security best practices.
Real-Time network tracking and reporting
Our real-time status reports and activity tracking ensure that your IT team knows exactly what the progress is of the engagement, when it’s expected to be completed, as well as any preliminary findings that we’ve identified. We include an activity log that monitors all activities performed during the penetration test. Network teams can correlate our activities with their SOC and incident response procedures.

Attack simulation – Pre and Post breach
PTAS can perform pre- and post-breach simulations at any time within both the internal and external network environments.
Open Source Intelligence Gathering – Using information from the public Internet to contribute to engineer a successful attack against the environment, including employee names, email addresses and other data.
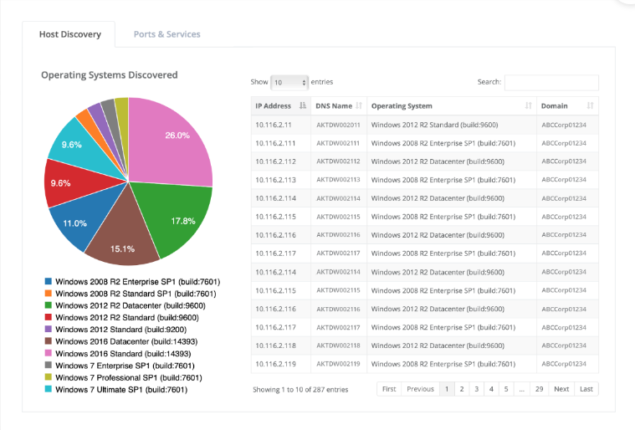
Host Discovery – Performing discovery of systems and services within the environment targeted, including active systems and port scanning.
Enumeration – Enumeration of services and systems to identify potentially valuable information, including vulnerability analysis.
Exploitation – Using information gathered from OSINT, host discovery, and enumeration, PTAS also launches attacks against vulnerable services, including password-based attacks, man-in-the-middle (MitM) attacks, relay attacks, and more.
Post-Exploitation – After gaining an initial foothold on a system, PTAS automatically attempts to launch privilege escalation attacks. Amicis will also analyse new attack avenues to determine if it can elevate its permissions within the environment to attack other services or access more sensitive data.
Finally, how does this work? The methodologies…
Egress Filter Testing:
PTAS automatically performs egress filtering to ensure that your organization is effectively restricting unnecessary outbound traffic. Unrestricted outbound access can allow a malicious actor to exfiltrate data from your organisation’s environment using traditional methods and unmonitored ports.
Authentication Attacks:
Upon the discovery of user account credentials, Amicis will automatically attempt to validate those credentials and determine where they are most useful. This is a common process executed by both malicious attackers and penetration testers and is performed during privilege escalation.
Privilege Escalation and Lateral Movement:
Using a valid set of credentials, Amicis will attempt to identify valuable areas within your organisation. We use a variety of methods, via our Amicis SecOps engine which assists in identifying where sensitive targets are.
Data Exfiltration:
Critical data leaving your organisation is an extremely serious concern. If weaknesses exist which threat actors can use to access confidential and/or sensitive data, Amicis will simulate and log this activity to help your organisation tighten areas that should restrict data exfiltration.
Simulated Malware:
With elevated access, Amicis will attempt to upload malicious code onto remote systems to test the organisation’s end-point anti-malware controls.
Efficient reporting:
Amicis’ PTAS generates an executive summary, technical and vulnerability report within 48 hours after the penetration test is complete. Our detailed deliverables will allow your IT team to cross reference our activities with monitoring and alerting controls.
Internal Vs External:
We offer two different PTAS options to support you in establishing greater security posture and operational resilience.
Internal – Using a device connected to your internal environment, our team will discover security vulnerabilities present within the internal network environment. These activities simulate that of a malicious attacker.
External – Assuming the role of a malicious attacker from the public Internet, our team will identify security flaws within your external network environment. These flaws can include patching, configuration, and authentication issues.
To learn more about how we’re saving our clients thousands of £’s in costs and months in lead time, without any compromise on output validity or quality, get in touch here or email us at hello@amicisgroup.co.uk
